PHIPA Administrative Monetary Penalty
436 Patient Records. One Clerk. A $2,000 Fine. What Your Organization Needs to Know.
PHIPA Decision 334 from the Information and Privacy Commissioner of Ontario is a wake-up call for every health organization.
A hospital clerk spent six months snooping through the personal health information of 436 patients. She lost her job and was personally fined $2,000.
The message is clear: having privacy policies on paper is not enough. Organizations must ensure that staff understand and follow those policies—and be able to prove it. When they cannot, patients lose trust and organizations face increased regulatory scrutiny
Privacy Breach Nuggets takes real cases and turns them into practical lessons for privacy officers, organizations, and healthcare or public sector institutions. Let’s break down what happened, what the decision found, and how these lessons apply to privacy and records management programs.
What Happened
A patient services clerk at the Children’s Hospital of Eastern Ontario (CHEO) inappropriately accessed the personal health information (PHI) of 436 patients between March and September 2024. The breach came to light when a nurse contacted CHEO’s Privacy Office with questions about her stepchild’s care. The Privacy Office became concerned about how the nurse appeared to know information she should not have known. An audit revealed that a clerk working in the same unit had accessed the child’s record without authorization.
A broader investigation showed that the clerk had accessed:
- Her own health record
- Family members’ records
- Hundreds of other patient records
The information viewed included demographic details, appointment histories, clinical notes, test results, and referral information.
Managing the Breach
We can analyze the hospitals and clinic’s response using the 4-Step Response Plan.
Step 1 – Spot and Stop
The first step is to recognize that a privacy breach has occurred and immediately stop further unauthorized access.
A privacy breach occurs when personal health information is lost, accessed, used, disclosed, or destroyed without authorization.
In this case, CHEO’s Privacy Office received a tip on September 10, 2024, when a nurse raised concerns about her stepchild’s health information.
Step 2 – Investigate
CHEO acted quickly:
- Conducted an initial audit
- Placed the clerk on administrative leave
- Revoked access to the electronic health record system
- Expanded the audit to six months of activity
- Conducted formal interviews and justification exercises
The investigation confirmed that the clerk had accessed 436 patient records without authorization.
There was no evidence that she copied, disclosed, or financially benefited from the information.
Remember: Simply viewing a patient record without a legitimate need to know is a privacy breach.
CHEO also confirmed that the clerk had completed initial privacy training and had signed a confidentiality agreement upon hire and a renewal in January 2023.
Step 3 – Notify
When a privacy breach occurs, the right people must be informed promptly.
Internally, notify your Privacy Officer and Custodian immediately.
CHEO reported the breach to the Ontario IPC on October 15, 2024.
CHEO initially notified 189 affected patients by mail. After a more extensive audit identified additional affected individuals, the hospital sent a further 107 notification letters in April 2025. Where current addresses were unavailable, notification letters were added to patient files for delivery at the next visit.
Step 4 – Prevent the Breach from Happening Again
After containing the incident, organizations must take steps to reduce the likelihood of recurrence.
CHEO:
- Implemented their progressive discipline process.
- Terminated the clerk’s employment on October 24, 2024.
- Conducted proactive audits twice monthly for six months.
- Implemented a comprehensive staff re-training initiative.
- Reinforced the importance of appropriate access and confidentiality.
Commissioner’s Investigation
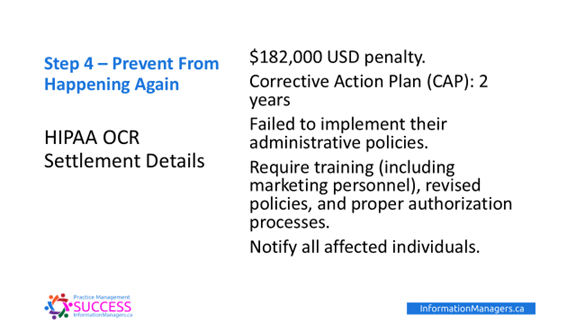
The Ontario IPC reviewed the incident and imposed Ontario’s second Administrative Monetary Penalty (AMP) under PHIPA.
An AMP is a financial penalty that the IPC can impose without commencing a court prosecution. The purpose is to encourage compliance and ensure that individuals or organizations do not benefit from privacy violations.
Under the PHIPA AMP regulations:
- Individuals may be fined up to $50,000
- Organizations may be fined up to $500,000
In this case, the clerk was ordered to pay $2,000 personally.
CHEO was not fined, but the Commissioner issued two formal recommendations to improve the organization’s ability to monitor, track, and document:
- Annual privacy training completion
- Annual confidentiality agreement renewals
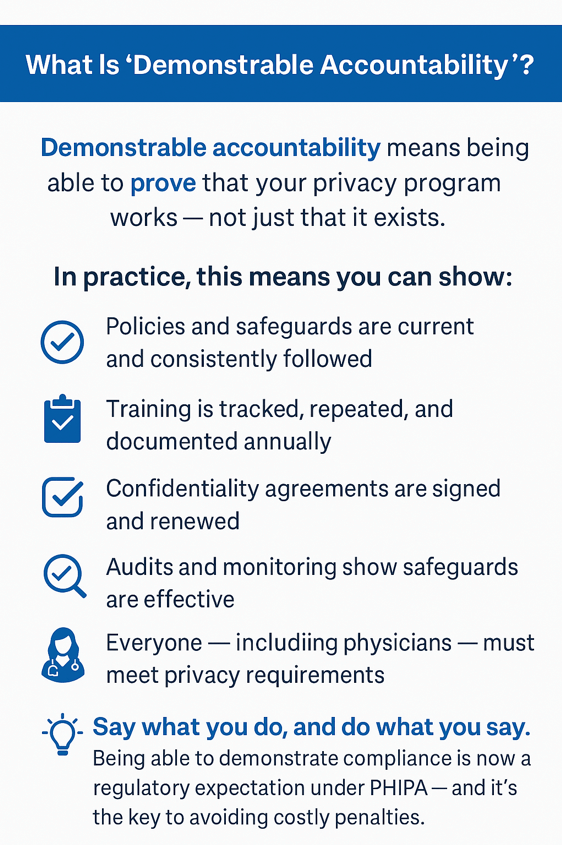
Demonstrable Accountability
One of the most important lessons from this decision is the concept of demonstrable accountability.
It is not enough to say that staff are trained and confidentiality agreements are renewed annually.
You must be able to prove it.
In this case, CHEO had strong privacy policies and procedures, but it could not produce documented evidence that the employee had completed her 2024 privacy training or re-signed confidentiality agreements in 2023 and 2024.
The Commissioner summarized this principle clearly:
Organizations must “say what they will do, and then do what they say.”
Take-Aways
✅ A privacy breach can start with one suspicious question–train staff to pay attention and speak up.
✅ Having privacy policies is not enough; you must be able to prove your staff are following them.
✅ Track and document annual privacy training and confidentiality agreement renewals for every single staff member.
✅ Curiosity snooping is a serious breach, even when there is no intention to disclose the information.
✅ Simply viewing a patient record without a legitimate need to know is a privacy breach.
Call to action
Want to strengthen your privacy breach response and accountability program?
Join Kayla Das and Jean L. Eaton for our How to Manage a Privacy Breach in Your Canadian Practice Workshop, where we provide practical tools, templates, and training to help your organization respond confidently to privacy incidents and demonstrate compliance.
Reference
Information and Privacy Commissioner of Ontario. PHIPA Decision 334. April 23, 2026. https://decisions.ipc.on.ca/ipc-cipvp/phipa/en/522336/1/document.do